You often see devices talk to each other with Wi-Fi, Bluetooth, Zigbee, LoRa, and cellular networks. These IoT communication protocols help devices connect and share data fast and safely. Many smart systems use MQTT, CoAP, HTTP, and MQTT-SN to send information. These protocols give you standard ways to send messages, keep your data safe, and help everything work together. You can see their main features in the table below:
Protocol | Description | Primary Function |
|---|---|---|
MQTT | Lightweight, publish-subscribe for low-bandwidth networks | Reliable message delivery with minimal bandwidth |
HTTP | Common for web data transfer | Device and server communication |
CoAP | For low-power, constrained devices | Interactive, low-power network communication |
DDS | Middleware for data-centric connectivity | Real-time, scalable data exchanges |
WebSocket | Full-duplex over single TCP | Real-time device-server interaction |
AMQP | Open standard for message passing | Reliable, robust messaging |
XMPP | Real-time communication and data exchange | Immediate feedback and interactivity |
OPC UA | Industrial machine-to-machine communication | Secure, reliable industrial data exchange |
You need to know how these protocols work to get the most from IoT and use data to make smart choices. Companies like Arshon Technology lead by making protocol integration and security better.
IoT Communication Protocols
Common IoT Communication Protocols
Many devices use different protocols to share data. These protocols help sensors, machines, and computers connect in smart systems. Learning about these protocols helps you pick the best way for your devices to talk.
Here is a table that shows the main features and technical details of popular IoT communication protocols:
Protocol | Characteristics | Technical Specifications |
|---|---|---|
MQTT | Works well in low bandwidth and resource-limited places | Uses TCP/IP, needs connection setup |
CoAP | Good for small devices and simple networks | Uses UDP, has a small header, no connection needed |
AMQP | Handles messages in queues for asynchronous communication | Flexible for IoT, supports message queuing |
XMPP | Uses XML, started for instant messaging | Higher overhead, not for memory-limited devices |
WebSocket | Allows two-way communication in real time | Sets up a connection, low overhead after setup |
DDS | Supports real-time, peer-to-peer communication | Uses publish/subscribe, efficient for distributed systems |
OPC UA | Handles complex data models and types | Advanced, fits industrial applications |
Each protocol has its own special features. MQTT and CoAP are good for simple and quick communication. AMQP and DDS help send messages even if the network is not perfect. OPC UA is strong for factories because it works with many kinds of data.
Tip: To help your devices work together, choose the right protocol. MQTT and CoAP are better for small sensors. OPC UA is good for big machines in factories.
These protocols help devices share data safely and reliably. AMQP uses message routing and supports encryption with TLS. MQTT works over TCP/IP, which helps when networks are not stable. DDS lets devices share data directly, making things fast. OPC UA supports safe and reliable data exchange in factories.
Using these protocols helps stop problems like lost messages or unsafe data. It also makes sure your system follows IoT standards, which are important for safety and working together.
Protocol Layers
It is important to know how protocol layers work in IoT. Each layer has a job, and together they help devices collect, send, and use data.
Here is a table that shows the main protocol layers in IoT communication:
Layer | Function |
|---|---|
Sensing Layer | Collects data from sensors and actuators |
Network Layer | Connects devices using networking protocols like WiFi, Bluetooth, and cellular networks |
Data Processing Layer | Analyzes and manages data from IoT devices |
Application Layer | Lets you control devices and see data through apps and dashboards |
The sensing layer gathers information. The network layer moves data between devices. The data processing layer helps you understand the data. The application layer lets you control devices and see results.
You can compare these layers to the OSI model and TCP/IP stack. The OSI model has seven layers. The TCP/IP stack has four layers. Both models help organize communication tasks. The TCP/IP stack is more useful for real IoT systems.
Application layer protocols in IoT match the top layers of the OSI model.
Network layer protocols handle connections and moving data.
The sensing layer is special to IoT and collects data.
Knowing how these layers work together helps you design better IoT systems. You make sure devices use the right protocols and follow standards. This helps build systems that are safe, reliable, and easy to manage.
Applications and Use Cases
Predictive Maintenance
Predictive maintenance is used in many industries today. It helps stop machines from breaking down without warning. This keeps machines working well. IoT communication protocols help collect data from sensors in real time. These protocols send information about machine health, temperature, vibration, and how much machines are used. Predictive maintenance technology looks at this data. It helps you know when a machine could break.
The predictive maintenance market is growing fast. Companies want to save money and have less downtime. You can find predictive maintenance in factories, farms, and vending machines. These systems watch equipment and warn you before something goes wrong.
Here is a table that shows which IoT protocols are best for predictive maintenance:
Protocol | Advantages | Use Cases |
|---|---|---|
LoRaWAN | Long-range, low power, good for small data packets | Remote monitoring, pipeline and tank level monitoring |
NB-IoT | Cellular-based, works well indoors | Smart utility metering, cold chain monitoring |
DigiMesh | Mesh network, works in changing places | Factory automation, mining and tunneling |
BMW uses IoT sensors to watch robots and predict problems. Siemens uses AI and predictive maintenance for wind turbines. This helps fix things before they break. Farmers use predictive maintenance to keep machines working and grow more crops. The market has solutions for coffee machines, dairy farms, and other places.
Tip: Predictive maintenance helps you plan repairs. It saves money and keeps your business running.
Industrial Automation
IoT communication protocols help make industrial automation work. These protocols connect machines, sensors, and control systems. You get real-time data from every part of your factory. This data helps you make quick choices and work better.
Industrial protocols let you use advanced automation systems. You can watch machines, control production lines, and check how things are working. These systems also help with predictive maintenance. You can fix problems before they stop production.
Here is a table that shows the good and hard parts of using IoT protocols in industrial automation:
Benefits | Challenges |
|---|---|
Better real-time monitoring | Data security worries |
More efficiency | Hard to connect with old systems |
Predictive maintenance | High starting costs |
Better choices with analytics | Lots of data to manage |
You see industrial automation in factories, mines, and farms. IoT protocols help connect old machines to new systems. You get predictive maintenance that keeps everything working well.
Real-Time Messaging
Real-time messaging helps your IoT systems respond fast. Protocols like MQTT and Kafka send messages quickly. You get real-time data from sensors and devices. This helps you act fast.
MQTT uses a publish/subscribe model. Devices send messages to a broker. You get updates right away. This protocol has three levels of Quality of Service. You know your messages arrive safely. Real-time messaging protocols keep a steady connection between client and server. You get fast, two-way communication. This is important for smart cities and healthcare.
Real-time messaging protocols help send messages well.
You can handle lots of small messages quickly.
The publish/subscribe model lets you share messages fast.
Note: Real-time messaging helps you watch systems, act in emergencies, and keep everything connected.
Security in IoT Protocols

Threats
There are many security problems with iot communication protocols. Hackers like to attack these systems. Many devices send data without any protection. This makes it easy for hackers to steal messages. Cyberattacks on IoT have gone up by 400% in one year. Factories now get about 6,000 attacks on their devices every week. Almost all IoT device traffic—98%—is not protected, so your data can be stolen.
Some common problems are:
Bad asset management leaves devices open for attacks.
No monitoring means you might miss strange activity.
Sending data without protection lets hackers listen in.
IoT botnets use your devices to make big attacks.
DNS threats happen when old devices join new networks.
Malicious node injection lets fake devices steal or change data.
Ransomware locks your devices or takes your data.
Physical tampering lets someone put bad software on your device.
Firmware exploits use weak spots in device software.
Note: If devices and servers talk without protection, hackers can listen, change messages, or add bad code.
Measures
You can keep your iot communication protocols safe with strong security steps. Use end-to-end encryption to protect your data from start to finish. Pick strong encryption like AES or RSA.
It is important to check who is using your system. Multi-factor authentication (MFA) needs more than one way to prove who you are. Digital certificates show that devices and users are real. Role-based access control (RBAC) lets each user or device do only certain things. This lowers the chance of someone inside causing trouble.
Here is a table that shows how security steps help:
Security Measure | Effectiveness |
|---|---|
Device Authentication | Stops fake devices from joining your network. |
Data Encryption | Keeps your data secret while it moves. |
Firmware Updates and Patches | Fixes weak spots and keeps your devices safe. |
Role-Based Access Control (RBAC) | Limits what users and devices can do, lowering risk. |
Incident Response Planning | Helps you act fast if something bad happens. |
Tip: Always update your devices and use strong passwords to keep your IoT system safe.
Networking Standards
Interoperability
You want your IoT devices to work together, even if they are from different brands. Interoperability means devices and systems can share data and understand each other. This is important for smart homes, cities, and factories.
A study by McKinsey says you can get up to 40% more value from IoT when devices work well together. But there are many problems you might face:
Multiple Communication Standards: Devices use Wi-Fi, Zigbee, Bluetooth, and others. This makes it hard to connect everything.
Lack of Common Standards: There are no rules that all devices follow. Some devices cannot talk to each other.
Proprietary Ecosystems: Some brands make closed systems. This can lock you into one company.
Security and Privacy Conflicts: Different security setups can make weak spots.
Complex Data Formats: Devices may need help to understand each other’s data.
Rapid Technology Changes: Standards can change fast and become old.
Cost and Resource Limits: Small companies may not have enough money or people.
When you add more IoT systems, the network gets more complex. This makes security harder. Each new device or protocol can bring new risks. The whole network can be easier to attack.
You can make interoperability better by using standard protocols like MQTT, CoAP, and HTTP. Groups like the Open Connectivity Foundation and the Industrial Internet Consortium help set these rules. APIs and IoT gateways also help devices with different protocols talk to each other.
Device Compatibility
Device compatibility means your IoT devices can connect and work as they should. You need to check for certifications and standards before adding new devices. Many companies and phone networks want devices to pass tough tests.
Certification Type | Description |
|---|---|
Verizon’s Certification | Needs FCC and GCF certifications, supports OTA updates, ongoing monitoring. |
AT&T’s Certification | Devices must be IoT Network Certified, pass signal and performance tests. |
T-Mobile’s Certification | Requires FCC and PTCRB certifications, uses approved modems, safety tested. |
Regulatory Certification | Covers electrical safety, RF emissions, and environment (e.g., FCC Part 15B). |
Telecom Certification | Includes GCF and PTCRB, ensures mobile network standards. |
Operator Certification | Operators can block non-compliant devices to protect network quality. |
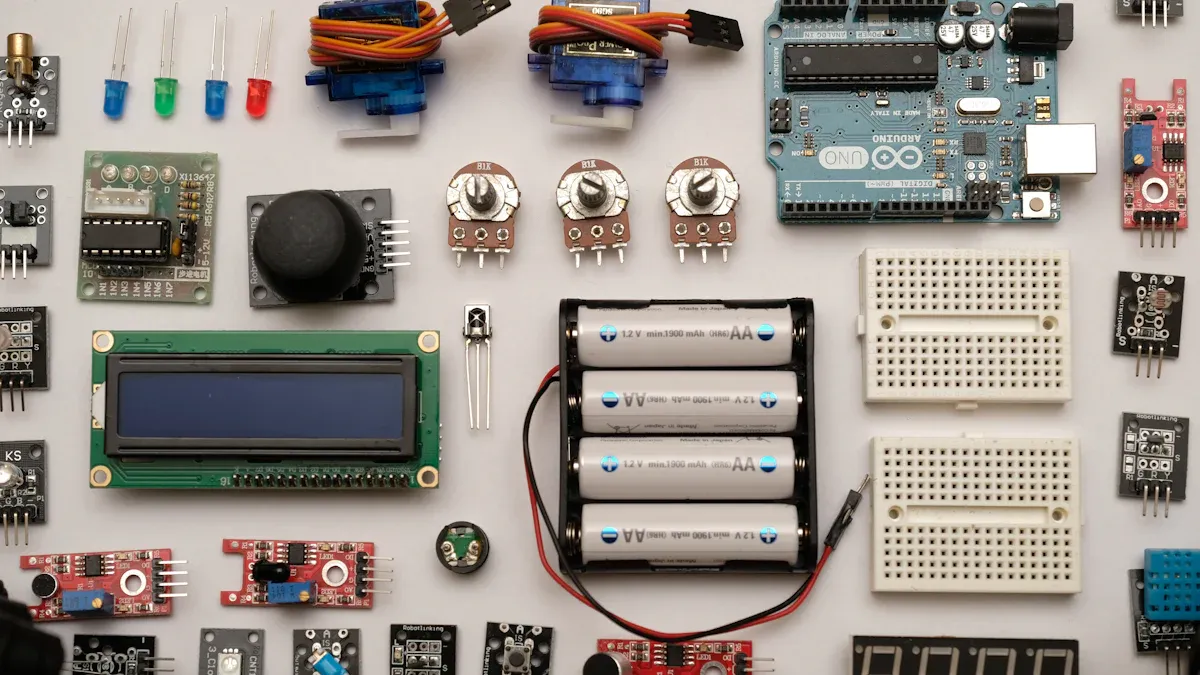
You should also think about protocol features. LoRaWAN and Sigfox help devices save battery, which is good for city sensors. Bluetooth Low Energy is great for wearables. ZigBee works well for smart homes. Picking the right protocol and certified devices helps you build a safe and strong IoT system.
Industry Contributions
Protocol Integration
There are many devices in the IoT world. Each device might use its own protocol. This makes it hard for devices to work together. Companies like Arshon Technology help fix this problem. They make sure devices can connect and share data easily. You get help from their skills with MQTT, CoAP, and DDS. Their solutions let devices talk, even if they are from different brands. This means your devices can work together, no matter the system.
Arshon Technology is known for protocol integration. They help your IoT devices work well and stay safe. Using their solutions gives you better connections and fewer problems. Their work helps smart homes, factories, and cities share data. As more devices join IoT, you need experts to handle the hard parts. They keep everything working without trouble.
Picking a company with good protocol integration makes your IoT system stronger and easier to use.
Innovation
New ideas and technology change IoT every year. Leaders in the industry work to make protocols safer and faster. They add strong encryption and ways to check who is using the system. These changes keep your data safe from hackers.
Some new security features are:
End-to-end encryption with TLS, AES, or DTLS
Device authentication using certificates or tokens
Secure boot and encrypted OTA updates
Intrusion detection systems and firewalls
Data checks and tamper protection
You also see new protocols made just for IoT. Old ones like HTTP cannot handle so many devices. Now, there are special protocols for IoT needs. These new standards help devices connect quickly and safely. As IoT grows, you will see more new ideas that make devices smarter and safer.
You need to know about iot communication protocols to make strong and safe systems. Experts say picking the right protocol helps your projects grow and work better. More devices use MQTT and CoAP every year. The table below explains why learning these protocols is important:
Key Takeaway | Description |
|---|---|
No one-size-fits-all protocol | 73% of experts said using different data formats and protocols made it hard to grow their projects. |
Increased adoption of purpose-made protocols | More connections will use IoT-specific protocols soon, with MQTT and CoAP growing the most. |
Importance of software in managing connectivity | Picking the right protocol helps your system work faster, stay safe, and use less power. |
Keeping up with new changes helps your devices work well and stay safe. You make your system safer by updating it often. You get better results with new analytics tools. You help devices share data and work together.
Industry leaders want safer and smarter systems. You should watch new trends to keep your IoT projects working well.
FAQ
What is the main purpose of IoT communication protocols?
IoT communication protocols help devices share information. They let devices talk to each other safely and fast. These protocols also help you control many devices in one place.
How do you choose the right protocol for your IoT project?
You need to think about what your devices need. Look at how big your network is and how much power you have. Some protocols are better for small sensors. Others are good for big machines. Always check if the protocol is safe and works with your devices.
Are IoT communication protocols secure?
Many protocols have security tools like encryption and authentication. You need to turn these tools on and keep your devices updated. This helps keep hackers away from your data.
Can different IoT devices use different protocols and still work together?
Yes, devices with different protocols can connect.
You use gateways or bridges to help them talk.
Standard protocols like MQTT and CoAP make this easier.