Have you ever wondered how engineers unlock the secrets hidden inside an integrated circuit (IC)? IC unlocking is the process of bypassing security features to access the internal data of an IC. It’s like finding the key to a locked treasure chest, revealing the intricate design and functionality within. This process plays a vital role in reverse engineering and programming. It allows you to analyze systems, optimize their performance, and even create innovative solutions.
The demand for IC unlocking has skyrocketed in recent years. The IC reverse engineering market, valued at $3.69 billion in 2024, is expected to grow to $9.32 billion by 2030. This rapid growth highlights how essential IC unlocking has become for engineers and programmers like you. Whether you’re troubleshooting a system or enhancing its compatibility, IC unlocking opens up endless possibilities.
Key Takeaways
IC unlocking helps engineers see inside chips to study them better.
Knowing the laws and ethics of IC unlocking is important to stay out of trouble and be honest.
Using methods like electronic tests and UV light can improve your skills in reverse engineering and creating new ideas.
IC unlocking can improve old systems by finding problems and making them better.
Mixing creativity with responsibility makes sure your work helps people and follows rules.
What is IC Unlocking?

Definition and Purpose of IC Unlock
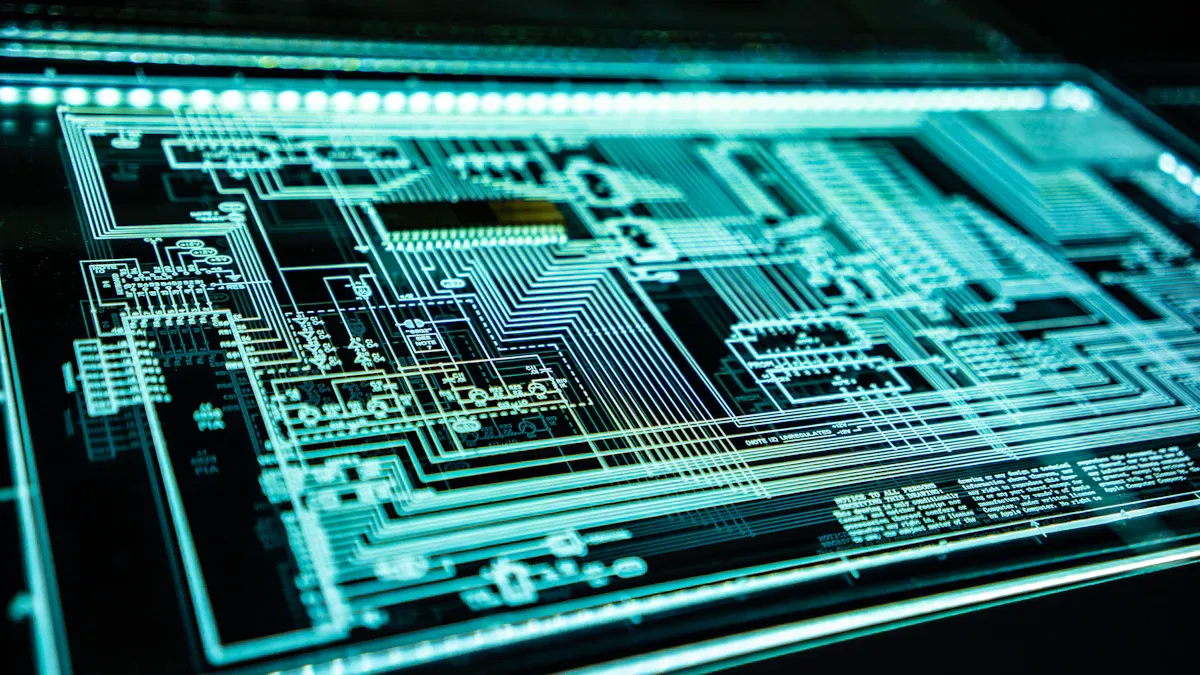
IC unlocking is the process of bypassing the security mechanisms of an integrated circuit (IC) to access its internal data or functionality. Think of it as cracking open a digital safe to uncover the secrets inside. This technique is widely used in reverse engineering to analyze and understand how a system works. It’s not just about breaking into a chip; it’s about learning from it.
The primary purpose of IC unlocking is to exploit vulnerabilities in chips to gain access to their data or features. Engineers use this process to study chip designs, extract firmware, and even optimize system performance. Some common methods include electronic detection attacks, error generation techniques, and probe technology. These approaches help engineers uncover hidden functionalities and improve existing systems.
How IC Unlocking Works
Unlocking an IC involves several technical steps. Here’s a simplified breakdown:
Understand the type of IC you’re working with.
Consider the legal and ethical implications of your work.
Gather the necessary tools and equipment.
Access the firmware stored in the IC.
Use reverse engineering techniques to analyze the chip’s design.
Modify the IC to achieve your desired outcome.
Document the entire process for future reference.
Each step requires precision and expertise. For example, accessing firmware might involve using UV attack methods to convert encrypted chips into non-encrypted ones. Reverse engineering helps you understand the chip’s architecture, while modification allows you to enhance its functionality.
Applications of IC Unlock in Engineering
IC unlocking has countless applications in engineering. It’s a powerful tool for troubleshooting, innovation, and system optimization. Here are some real-world examples:
Technique | Description |
|---|---|
Electronic Detection Attacks | Monitors the processor’s analog characteristics and electromagnetic radiation during operation to extract critical information. |
Error Generation Attack | Uses abnormal conditions to induce processor errors, allowing access to protected information through voltage and clock strikes. |
Probe Technology | Involves exposing chip internal connections to manipulate and interfere with the microcontroller. |
UV Attack Method | Applies ultraviolet radiation to convert encrypted chips into non-encrypted ones, allowing direct program reading, particularly effective for OTP chips. |
Chip Loopholes | Exploits cryptographic vulnerabilities in chip design to read out code in memory, such as using specific byte patterns to reverse engineer programs. |
These techniques demonstrate how IC unlocking can help you analyze systems, improve designs, and even innovate new technologies. Whether you’re working on legacy systems or cutting-edge devices, IC unlocking is a game-changer in reverse engineering.
Why IC Unlocking is Essential for IC Reverse Engineering
Understanding System Design Through Reverse Engineering
Reverse engineering gives you a unique opportunity to dive deep into the design of an integrated circuit. By unlocking an IC, you can uncover its architecture and functionality, which helps you understand how it operates. This process isn’t just about taking things apart; it’s about learning how every piece fits together.
Engineering Lifecycle Management (ELM) plays a big role here. It ensures that every stage of IC development—like requirements management, design data handling, and team collaboration—is well-documented and traceable. When you reverse engineer an IC, you gain insights into these stages, which improves your understanding of system design. This knowledge-sharing approach enhances product quality and reliability, making it easier for you to innovate or troubleshoot.
How to Reverse Engineer an IC for Innovation
Reverse engineering an IC for innovation involves several steps. Here’s how you can do it:
Gather tools like design software and layout extraction tools.
Examine the IC under a microscope to identify its components.
Take high-resolution images of the IC.
Use image recognition software to convert the images into a layout.
Extract the circuit netlist from the layout.
Create a schematic from the netlist to understand the circuit’s functionality.
You can also use techniques like delayering, imaging, and annotation to analyze the IC further. These methods help you uncover hidden features and inspire new ideas for your projects. By reverse engineering, you’re not just replicating; you’re innovating.
Analyzing and Improving Legacy Systems
Legacy systems often come with outdated ICs that need upgrades or repairs. IC unlocking allows you to reverse engineer these chips and breathe new life into old systems. You can analyze their design, identify inefficiencies, and make improvements.
For example, delayering and imaging techniques let you study the IC’s structure without damaging it. Once you understand its design, you can optimize its performance or even replace it with a modern equivalent. This process ensures that legacy systems remain functional and efficient, saving you time and resources.
Reverse engineering isn’t just about fixing problems. It’s about achieving the objectives of reverse engineering, like improving system reliability and extending the lifespan of older technologies. With IC unlocking, you can turn outdated systems into valuable assets.
Benefits of IC Unlocking in Programming
Debugging and Troubleshooting with IC Unlock
When you’re working on complex systems, debugging can feel like solving a giant puzzle. IC unlock makes this process much easier. By unlocking an IC, you gain access to advanced debugging tools that help you identify and fix issues faster. For example, tools like S2C’s Prodigy prototyping solution offer real-time control and deep debugging modules. These tools allow you to interact with real-world data and pinpoint design flaws effectively.
If you’re dealing with multi-FPGA setups, IC unlock can be a lifesaver. Tools like the MDM Pro let you probe signals and trigger functions across multiple chips at the same time. This means you can troubleshoot even the most complicated systems without breaking a sweat. With IC unlock, you’re not just fixing problems—you’re ensuring your program runs smoothly and efficiently.
Firmware Extraction and System Optimization
Firmware is the brain of any IC. Unlocking it gives you the power to extract and analyze its code. This is especially useful when you’re optimizing a system. By studying the firmware, you can identify inefficiencies and rewrite the code to improve performance.
Imagine you’re working on a legacy program. The firmware might be outdated or poorly written. With IC unlock, you can extract the code, make the necessary changes, and upload an optimized version. This process not only enhances the system’s functionality but also extends its lifespan. It’s like giving an old device a brand-new lease on life.
Enhancing Software Compatibility
Have you ever struggled to make a program work with a specific IC? IC unlock can help you solve this problem. By accessing the chip’s internal code, you can modify it to ensure compatibility with your software. This is especially important when you’re developing programs for devices with unique or proprietary ICs.
For example, you might need to adapt your program to work with a custom chip in a specialized device. IC unlock allows you to analyze the chip’s architecture and tweak your code accordingly. This ensures seamless integration and a better user experience. With IC unlock, you can bridge the gap between hardware and software, making your programs more versatile and reliable.
Risks and Ethical Considerations of IC Unlocking
Intellectual Property and Legal Concerns
IC unlocking can open doors to innovation, but it also comes with legal risks. When you bypass security features, you might unintentionally violate intellectual property laws. Many chips are protected by patents or copyrights, and accessing their internal data without permission could lead to legal consequences.
Before you start reverse engineering an IC, it’s crucial to understand the laws in your region. Some countries have strict regulations against circumventing security features, even for educational or research purposes. Always ensure that your work complies with local and international laws. This step not only protects you legally but also helps maintain the integrity of your engineering projects.
Ethical Practices in IC Reverse Engineering
When you unlock an IC, you’re stepping into a gray area that requires careful thought. Ethical practices are essential to ensure your work doesn’t harm others or lead to misuse. Here are some guidelines to follow:
Make sure your activities comply with laws related to reverse engineering and digital rights management.
Consider the impact of your work. Avoid actions that could infringe on intellectual property or enable malicious uses.
By following these principles, you can focus on gathering information responsibly and using it to improve systems or create new technologies. Ethical engineering isn’t just about following rules; it’s about making choices that benefit society.
Balancing Innovation and Responsibility
Unlocking an IC gives you the power to innovate, but it also comes with responsibility. The modification of chips can lead to groundbreaking advancements, but it’s important to weigh the potential risks. Ask yourself: Will this work improve a system or create vulnerabilities?
Balancing innovation with responsibility means thinking beyond the technical aspects. It’s about understanding the broader implications of your actions. When you approach IC unlocking with this mindset, you can contribute to the field of reverse engineering while maintaining ethical standards.
Tip: Always document your process and intentions. Transparency helps build trust and ensures your work aligns with ethical and legal guidelines.
Essential Tools and Techniques for IC Unlocking

Hardware-Based IC Unlock Methods
When it comes to unlocking an IC, hardware-based methods are some of the most effective tools in your arsenal. These techniques focus on physically interacting with the chip to bypass its security. Here are some common methods you can use:
FIB Recovery Encryption Fuse Method: This method restores the fuse in chips like TI’s MSP430 to unlock them.
Modifying the Encryption Circuit: By analyzing the chip’s structure, you can alter its encryption circuit to disable security.
Error Generation Attack Technology: This technique uses voltage or clock strikes to cause errors, giving you access to protected data.
Probe Technology: Expose the chip’s internal connections to manipulate and interfere with its microcontroller.
UV Attack Method: Apply ultraviolet light to erase encryption on OTP chips, making them readable.
Chip Loopholes: Exploit cryptographic vulnerabilities in the chip’s design to extract memory data.
These methods require precision and the right tools, but they’re invaluable for reverse engineering projects.
Software Techniques for IC Reverse Engineering
Software techniques are just as important as hardware methods. They allow you to analyze and understand the IC’s design without physically altering it. Here’s how you can get started:
Delayering: Remove layers of the IC using plasma or wet etching to expose its internal structure.
Imaging: Use optical or scanning electron microscopy (SEM) to capture detailed images of the IC.
Annotation: Stitch images together to extract the circuit layout, either manually or automatically.
Schematic Creation: Perform design rule checks to identify errors and create a schematic.
Schematic Analysis: Use open data sources to understand the circuit’s functionality.
Advanced tools like MITRE’s Pix2Net™ v2.0 automate these processes, making reverse engineering faster and more accurate.
Essential Tools for Engineers and Programmers
To unlock an IC effectively, you need the right tools. Here’s a quick overview of what you’ll need:
Tool Type | Description |
|---|---|
Programmer and Debugger | Use devices like JTAG programmers to interface directly with the IC. |
Software Tools | Tools like IDA Pro or Hopper act as disassemblers for analyzing firmware. |
Probe technology is another essential tool. It lets you expose and manipulate the chip’s internal connections, giving you greater control over the unlocking process. With these tools, you’ll have everything you need to tackle even the most complex ICs.
IC unlocking is more than just a technical process; it’s a gateway to understanding, improving, and innovating systems. By unlocking an IC, you gain the ability to dive deep into its design, optimize its performance, and even extend its lifespan. This makes it an essential tool in reverse engineering, helping you uncover hidden potential in both modern and legacy systems.
However, with great power comes great responsibility. Ethical practices ensure that your work benefits society while respecting intellectual property and legal boundaries. Here’s how ethical IC unlocking can drive innovation responsibly:
Key Takeaways | Description |
|---|---|
Comprehensive Understanding | Learn the importance of ethical and responsible practices in engineering and programming. |
Best Practices | Follow principles that balance innovation with accountability. |
Real-World Applications | See how ethical approaches lead to practical, impactful solutions in reverse engineering. |
When you approach IC unlocking with a focus on ethics and responsibility, you not only innovate but also contribute to a more secure and sustainable tech landscape. So, as you explore the possibilities, remember to balance creativity with accountability. That’s how you truly unlock the future.
FAQ
What is the difference between IC unlocking and reverse engineering?
IC unlocking focuses on bypassing security to access internal data, while reverse engineering involves analyzing the entire system to understand its design and functionality. Unlocking is often a step within reverse engineering. Think of it as opening a door to explore what’s inside. 🚪
Is IC unlocking legal?
It depends on your location and purpose. Some countries allow IC unlocking for research or educational purposes, while others have strict laws against it. Always check local regulations and ensure you have permission before starting. Staying informed protects you from legal trouble. ⚖️
Can IC unlocking damage the chip?
Yes, it can. Techniques like UV attacks or probe technology may physically alter or harm the chip. To minimize risks, use precise tools and follow best practices. If you’re new to this, start with less invasive methods to avoid costly mistakes. 🛠️
What tools do I need for IC unlocking?
You’ll need hardware tools like JTAG programmers and software tools like IDA Pro. For advanced tasks, consider microscopes for imaging and tools for delayering. Having the right equipment ensures accuracy and efficiency in your work. 🖥️
Why is ethical IC unlocking important?
Ethical unlocking ensures your work benefits society without harming others or violating intellectual property. It’s about balancing innovation with responsibility. By following ethical practices, you contribute to a secure and sustainable tech landscape. 🌍