Have you ever wondered how something works by taking it apart? That’s the essence of reverse engineering. It’s a method used to break down systems, products, or software to understand their inner workings. Industries like software development, mechanical engineering, and electronics rely on this approach to tackle challenges. For example, reverse engineering helps recreate outdated technology, improve interoperability, and even identify security vulnerabilities. Techniques like PCB copy and IC unlock are often used to analyze electronic components, making it easier to troubleshoot or enhance designs. Whether you’re solving a problem or learning from an existing solution, reverse engineering gives you the tools to dig deeper and uncover valuable insights.
Key Takeaways
Reverse engineering shows how things work by taking them apart. It is helpful in areas like coding and making products.
To reverse engineer well, first decide your problem or goal. This will keep you focused and save time.
Learn all you can about the system before taking it apart. Use guides and tools to gather helpful information.
Testing ideas is very important. Check your guesses with tests to make sure they work.
Stay neat and write down what you find as you go. This helps you remember your work and improve it later.
What Is Reverse Engineering and Why Is It Useful?
Definition and Core Principles
Reverse engineering is the process of analyzing a system, product, or software to understand how it works. It involves breaking down the components and studying their interactions to uncover the underlying design or functionality. The process typically follows three core principles: information extraction, modeling, and review. First, you gather all relevant data about the system. Then, you create an abstract model that represents how the system operates. Finally, you test and refine the model to ensure its accuracy. This structured approach makes reverse engineering a powerful tool for solving problems and improving designs.
Common Applications in Real-World Scenarios
Software Development and Debugging
In software development, reverse engineering helps you analyze existing code to identify bugs or optimize performance. For example, developers often use tools like debuggers and disassemblers to understand how a program executes. This approach is also crucial for identifying common security vulnerabilities in software, such as buffer overflows or weak encryption methods.
Product Design and Innovation
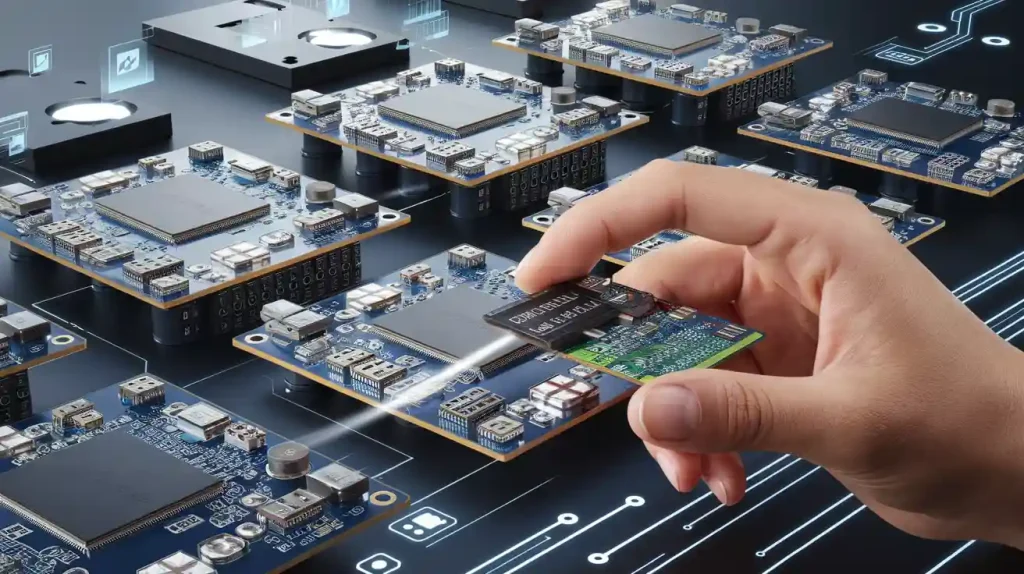
Reverse engineering plays a significant role in product design. Companies often study competitors’ products to learn from their designs and improve their own. For instance, Tesla’s competitors, like Rivian and Lucid Motors, reverse-engineer Tesla vehicles to analyze battery technology and enhance their electric vehicle designs. Techniques like PCB copy and IC Unlock are commonly used to replicate and refine electronic components.
Cybersecurity and Vulnerability Analysis
In the world of cyber-security, reverse engineering is essential for identifying and addressing vulnerabilities. Security researchers often reverse-engineer malware to understand its attack methods and develop countermeasures. A famous example is the analysis of the Stuxnet malware, which revealed its sophisticated mechanisms and helped improve defenses against similar threats.
Benefits of Reverse Engineering in Problem-Solving
Reverse engineering offers several benefits when tackling challenges. It allows you to understand complex systems without relying on documentation, which is often unavailable. By deconstructing a system, you can identify inefficiencies, improve functionality, and even innovate entirely new solutions. For example, during the Cold War, the U.S. reverse-engineered captured MiG fighter jets to enhance their aircraft designs. Similarly, reverse engineering helps uncover common security vulnerabilities, enabling you to strengthen defenses and protect sensitive systems.
Tools and Skills Needed for Reverse Engineering

Essential Tools for Reverse Engineering
Software Tools
To get started with reverse engineering, you’ll need the right software tools. These tools help you analyze and understand systems effectively. Here are some of the most commonly used ones:
Ghidra: This open-source framework, developed by the NSA, supports decompilation and collaborative reverse engineering.
Radare2: A modular tool for disassembly and debugging, perfect for various architectures.
OllyDbg: A debugger for Windows that allows you to analyze programs dynamically.
x64dbg: An open-source debugger with a user-friendly interface and scripting support.
IDA Pro: Known for its high-quality decompiler output, it’s a favorite among professionals.
Wireshark: While not a traditional reverse engineering tool, it’s excellent for analyzing network traffic and protocols.
These tools are essential for tasks like PCB copy and IC Unlock, especially when working with electronic components.
Hardware Tools
When working with physical systems, hardware tools are just as important. Here’s a quick look at some key tools and their applications:
Hardware Tool | Application Description |
|---|---|
Physical Examination | Disassembling hardware to inspect components. |
Using microscopes or X-ray imaging for internal analysis. | |
Mapping circuit traces and extracting firmware. | |
3D Scanning and Modeling | Creating digital models of physical parts. |
Circuit Tracing | Understanding electrical pathways in circuits. |
Material Analysis | Determining component durability and material properties. |
These tools help you dive deep into the physical aspects of reverse engineering, making it easier to analyze and replicate designs.
Key Skills for Success
Programming and Coding Knowledge
You’ll need a solid understanding of programming languages like C, Python, or Java. This knowledge helps you analyze software systems and modify code when necessary.
Analytical Thinking and Problem-Solving
Reverse engineering requires you to think critically. Techniques like dynamic analysis and 3D modeling help you break down complex systems into manageable parts.
Understanding of System Architecture
Knowing how systems are built is crucial. Whether it’s software or hardware, understanding the architecture helps you map out interactions and dependencies effectively.
Recommended Resources for Learning
If you’re a beginner reverse engineer, there are plenty of tutorials and resources to help you get started:
Ghidra tutorials: These are great for learning the basics of reverse engineering tools.
The Ghidra Book: The Definitive Guide: A must-read for mastering Ghidra.
Crackme challenges: Found on crackmes one, these are perfect for testing your skills.
Vulnhub: A platform for exploring security vulnerabilities.
CTFs (Capture The Flag): These challenges provide hands-on experience with reverse engineering.
These resources will help you build your skills and confidence as you explore the world of reverse engineering.
Step-by-Step Guide to Solving Problems with Reverse Engineering

Step 1: Identify the Problem or Goal
Before diving into reverse engineering, you need to define what you’re trying to achieve. Are you troubleshooting a malfunctioning device, analyzing malware, or improving a product design? Start by planning and preparing. Define the scope of your project and set clear objectives. For example:
Determine or propose an outcome.
Assess whether the system meets your expectations.
If it doesn’t, revisit the documentation to identify gaps and refine your analysis.
This step ensures you stay focused and avoid unnecessary detours.
Step 2: Gather Information About the System
Once you’ve set your goal, it’s time to collect as much information as possible about the system. This step is crucial for understanding what you’re working with. You can:
Review any available documentation, user manuals, or technical drawings.
Conduct pre-deconstruction audits to gather data from archives.
Inspect the system thoroughly for signs of wear, damage, or modifications.
Use tools like electronic measuring devices to take precise measurements.
Document your findings with photos, videos, and notes.
For example, when working on PCB copy or IC Unlock, you might compare the physical circuit board with its design schematics to spot any changes. This detailed preparation lays the groundwork for effective reverse engineering.
Step 3: Deconstruct the System
Now comes the exciting part—breaking the system down to understand how it works. This process involves two key steps:
Analyzing Components and Their Functions
Take the system apart piece by piece. Examine each component to figure out its role. For instance, in malware analysis, you might dissect the code to identify how it exploits vulnerabilities. Similarly, in back engineering a product, you could analyze the materials and design to understand its durability and functionality.
Mapping Interactions and Dependencies
Once you’ve identified the components, map out how they interact. Look for dependencies between parts. For example, in a security audit, you might trace how a vulnerability exploitation spreads through a network. This mapping helps you see the bigger picture and identify areas for improvement or replication.
By following these steps, you’ll gain a deeper understanding of the system and be ready to develop solutions or innovations.
Step 4: Develop Insights and Hypotheses
Once you’ve deconstructed the system, it’s time to connect the dots. Look at the components and their interactions to uncover patterns or potential issues. Ask yourself questions like, “Why was this design choice made?” or “How does this part contribute to the overall functionality?” These insights can help you form hypotheses about how the system works or why it might be failing.
For example, if you’re analyzing malware, you might notice a specific code segment that exploits vulnerabilities in a network. This could lead you to hypothesize how the malware spreads or targets specific systems. Similarly, when working on PCB copy or IC Unlock, you might identify areas where the circuit design could be optimized for better performance or cost efficiency.
Your hypotheses should be actionable. They should guide your next steps, whether you’re troubleshooting, improving a design, or replicating a system. Keep your findings organized and document your thought process. This will make it easier to test your ideas in the next step.
Step 5: Test and Implement Solutions
Now it’s time to put your hypotheses to the test. Use a systematic approach to validate your ideas and implement solutions. Here are some effective methods you can use:
Analysis of publicly available information: Gather data from accessible sources to compare your findings. This method is cost-effective but may not always provide complete insights.
Device, system, and applications testing: Test the system directly to assess its functionality. This hands-on approach can reveal valuable details but may require additional resources.
Reverse engineering: Dive deeper into the system to confirm your hypotheses. This method is resource-intensive but often provides critical information when other methods fall short.
For instance, if you’re addressing vulnerabilities in a software system, you might run simulations to see how the malware behaves under different conditions. If you’re working on an electronic product, you could prototype a modified PCB design to test its efficiency. Always document your results and refine your solutions based on what you learn.
Example Case Study: Reverse Engineering an Electronic Product
Understanding the Product’s Design and Functionality
In the mid-1980s, Phoenix Technologies successfully reverse-engineered the IBM BIOS to create a compatible BIOS for PCs. They used a “clean room” approach, where one team analyzed the IBM BIOS and documented its functionality. A separate team, unaware of the original code, developed a new BIOS based on these specifications. This method ensured they avoided copyright infringement while achieving a fully functional product.
When reverse engineering an electronic product, you can follow a similar approach. Start by studying the product’s design and functionality. For example, examine the PCB layout and use IC Unlock techniques to understand the chip’s internal workings. This will help you identify how the components work together and what makes the product unique.
Identifying Areas for Improvement or Replication
Once you understand the product, look for areas to improve or replicate. Could the design be more efficient? Are there features you can enhance? For example, you might find that a specific circuit could be simplified to reduce manufacturing costs. Or, you might discover a way to replicate the product for a different application. By focusing on these opportunities, you can create innovative solutions or competitive alternatives.
Challenges and Best Practices in Reverse Engineering
Common Challenges
Complexity of Systems
Modern systems are often intricate, with advanced designs and technologies that can be overwhelming to analyze. For example, electronic products may include multilayered PCBs or encrypted ICs, making tasks like PCB copy or IC Unlock time-consuming and technically demanding. You might find yourself needing specialized tools or software to handle these complexities effectively.
Lack of Documentation
Sometimes, you’ll face a lack of access to original design documentation. This can make it harder to understand how a system works or to replicate its functionality. Without detailed schematics or manuals, you’ll need to rely on your skills and tools to piece together the missing information.
Legal and Ethical Concerns
Reverse engineering raises questions about intellectual property rights and ethical boundaries. For instance, software licensing agreements often restrict reverse engineering practices. To avoid legal risks, you should conduct a Freedom-to-Operate (FTO) search and review any contractual obligations. Consulting legal counsel can also help you navigate these challenges responsibly.
Best Practices for Success
Stay Organized and Document Findings
Keeping detailed records of your process is essential. Use photos, notes, and diagrams to document each step. This not only helps you stay organized but also makes it easier to revisit your findings later. For example, when working on PCB copy or IC Unlock, documenting the circuit layout and component details can save you time during replication or troubleshooting.
Collaborate with Experts When Needed
You don’t have to tackle everything alone. Collaborating with experts, such as data scientists or hardware engineers, can significantly enhance your project’s success. For instance, a team of specialists once used advanced neural networks to improve the performance of an AI-based system, enabling it to track flying targets in real-life conditions. Their combined expertise made the project a success.
Adhere to Ethical and Legal Guidelines
Always prioritize ethical practices. Avoid violating contract laws or intellectual property rights. Conducting an FTO search and consulting legal experts can help you stay within legal boundaries. Following these guidelines ensures your work remains both lawful and ethical.
Reverse engineering opens up endless possibilities for solving problems and driving innovation. If you’re just starting, focus on small projects and build your skills step by step. Here’s a quick roadmap to help you:
Learn assembly language to understand the basics.
Get familiar with file formats like PE and ELF.
Practice using tools like Ghidra and IDA.
Debug programs with tools such as GDB or x64dbg.
Take on real-world challenges like CTFs to sharpen your skills.
As you progress, engage in hands-on activities like PCB copy or IC Unlock to deepen your understanding of electronic systems. Always document your process and stay curious. Reverse engineering is a field that rewards continuous learning and ethical practices. By mastering it, you’ll not only solve complex problems but also uncover opportunities for innovation.
Tip: Study successful products to learn their design logic and find ways to improve or replicate them.
FAQ
What is PCB copy, and why is it important in reverse engineering?
PCB copy involves analyzing and replicating a printed circuit board’s design. It helps you understand how electronic components interact. This process is crucial for troubleshooting, improving designs, or creating compatible alternatives. It’s a key step in reverse engineering electronic products.
How does IC Unlock help in reverse engineering?
IC Unlock allows you to access the internal structure of an integrated circuit. By understanding its design, you can analyze functionality, identify vulnerabilities, or replicate features. This technique is especially useful when documentation is unavailable or incomplete.
Is reverse engineering legal?
Reverse engineering is legal in many cases, but it depends on your purpose and local laws. For example, using PCB copy or IC Unlock for educational purposes is often allowed. However, replicating patented designs without permission can lead to legal issues. Always consult legal experts.
Can I reverse-engineer a product without advanced tools?
Yes, you can start with basic tools like screwdrivers, multimeters, or free software like Ghidra. For tasks like PCB copy or IC Unlock, you’ll need specialized tools. Start small, and as you gain experience, invest in advanced equipment to tackle complex projects.
How do I get started with reverse engineering?
Begin by learning the basics of system architecture and programming. Practice with simple projects like analyzing old electronics. Use tools like Ghidra or IDA for software and basic hardware tools for physical systems. Explore techniques like PCB copy and IC Unlock to deepen your skills.
💡 Tip: Start with open-source projects or outdated devices to practice reverse engineering legally and safely.