You can see how cybersecurity firewalls keep your network safe. They do this by putting up strong barriers. Security policy lets you make clear rules for your plan. Layered defense makes sure threats meet many blocks. Industrial firewall solutions help keep factories and important systems safe. PCB design and manufacturing are important for making each firewall work well.
When you follow these steps, you make your system safer and better.
Key Takeaways
Begin with a clear security policy. It tells what to protect. It shows who can use your network.
Use many defense layers to make security better. If one layer fails, others help protect you.
Pick the best firewall for your network. Use hardware for big networks. Use software for single devices.
Change firewall rules often to stop new threats. This keeps your protection strong.
Choose good PCB materials for firewalls. This helps data move fast. It also makes firewalls work well.
Cybersecurity Firewalls Principles
Security Policy and Layered Defense
You should begin with a strong security policy for firewalls. This policy helps you pick what to protect. It tells you who can use your network and what they can do. Security requirements help you choose the right firewall controls. You need to check your security needs before changing firewall settings.
A layered defense makes your network safer. You use many layers, like physical, technical, and administrative controls. Each layer adds more protection and blocks threats. If one layer fails, another layer helps you react. Do not trust only one firewall. Using different security tools and steps helps fill gaps and lowers the risk of a breach.
Tip: Using many layers and repeating security steps makes your cybersecurity stronger.
Types and Placement of Firewalls
You need to think about firewall types and where to put them. You can use hardware firewalls, software firewalls, or next-generation firewalls. Each type is good for different things. Place firewalls between network parts to catch threats early. Put internet-facing servers in their own zones to limit damage from attacks. Use one-way traffic rules between inside zones and DMZs. Keep web servers and database servers in separate DMZs. Send internet traffic through an HTTP proxy server in the main DMZ. Never let internet traffic go straight to your inside zone.
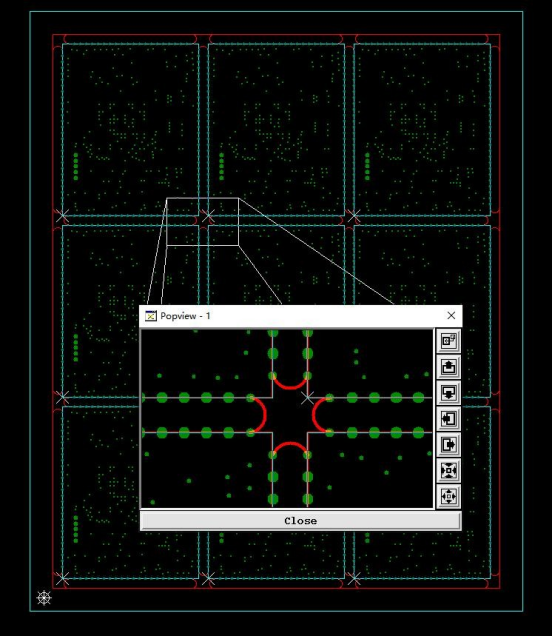
Multi-layer firewall management connects network parts safely.
Network segmentation helps you watch and control traffic.
Firewall management lets you change rules to fit your needs.
Industrial Firewall Features
Industrial firewalls keep factories and important systems safe. You should focus on devices, not just IP addresses, for strong security. Industrial firewalls handle high bandwidth and throughput. Use VPNs to keep remote users safe. In factories, firewall management must follow strict rules. Watch applications and user activity to stop threats. Next-generation firewalls check applications and devices for risks. Always update firewall rules to meet new security needs.
Note: Industrial firewall management needs updates and strong watching to keep your cybersecurity working well.
Firewall Design and Architecture

Planning and Strategic Approach
You begin by learning about your network. You look at a map of your network. You find what is important and what needs protection. You check for weak spots. This helps you know what to keep safe.
Next, you make a firewall policy. This policy controls what goes in and out. You pick the best firewall for your needs. You set up the firewall and test it. You keep checking the firewall to make sure it works.
Here are the main steps for planning firewall architecture:
Look at your network and find what matters most.
Make a firewall policy that fits your needs.
Choose the right firewall for your network.
Set up and test the firewall.
Keep checking and managing the firewall.
Firewall architecture can look different in different places. The table below shows how strategies change:
Aspect | Enterprise Environments | Industrial Environments |
|---|---|---|
Focus | Broader IT security measures and compliance | Operational Technology (OT) and integration with IT |
Firewall Placement | Generalized strategies for IT security | Specialized strategies for Industrial Control Systems (ICS) |
Security Approach | Emphasis on regulatory compliance and IT security | Focus on operational integrity and threat detection |
Complexity | Typically less complex due to standardized IT practices | More complex due to diverse systems and requirements |
Layered Security | Multi-layered security with various IT measures | Defense in depth with specific OT considerations |
Monitoring | Long-term monitoring for IT threats | Proactive engagement in threat detection and mitigation |
Tip: Match your firewall design to your environment for the best safety.
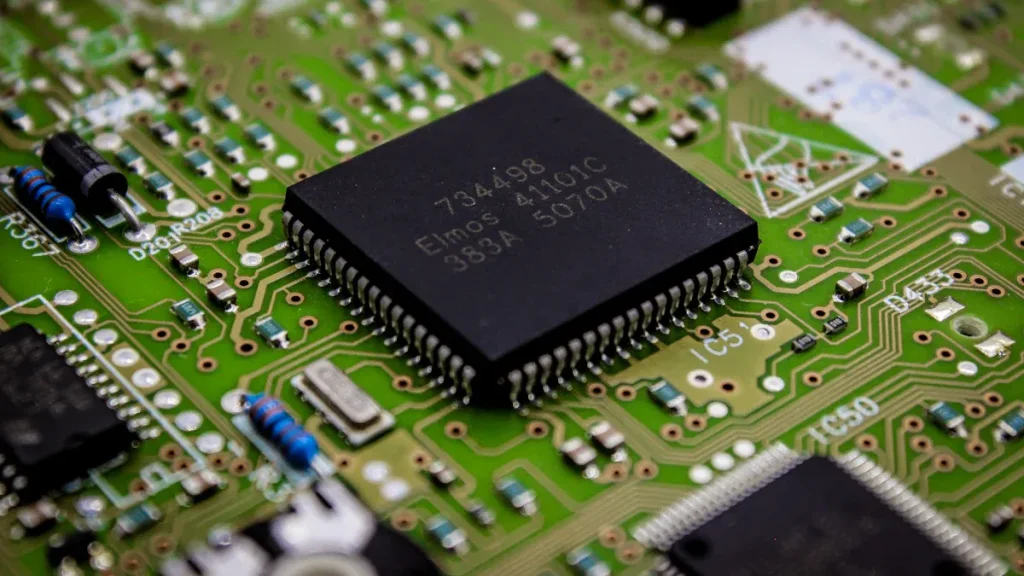
Core Components and PCB Design
A strong firewall needs the right parts. The main parts are processors, memory, network interfaces, and the PCB. The PCB connects all the parts so they work together.
Picking good PCB materials is very important. Good materials help data move faster. This lets your firewall handle more traffic. Good materials also help control heat. Your firewall stays safe even when busy. The right materials mean less signal loss and better threat detection.
Evidence Description | Impact on Firewall Performance and Durability |
|---|---|
High-quality PCB materials enhance data transmission speeds. | This leads to improved performance in handling network traffic and security protocols. |
Advanced PCB materials improve thermal conductivity and reduce heat accumulation. | This ensures stable operation under heavy loads, enhancing durability and reliability. |
Strategic material selection minimizes signal loss and enhances signal integrity. | This contributes to the firewall’s ability to detect and mitigate cyber threats effectively, ensuring long-term performance. |
Note: Always use the best PCB materials for a strong firewall.
Software vs. Hardware Firewalls
You can pick software or hardware firewalls. Each one has good and bad points. The table below helps you compare them:
Feature | Hardware Firewalls | Software Firewalls |
|---|---|---|
Deployment | Requires physical setup and maintenance | Easier to deploy across multiple devices |
Performance | Superior performance for high-volume traffic | Limited to the resources of the host |
Security Features | Advanced features like SSL inspection and VPN support | Basic functionality, often limited to port blocking |
Ideal Use Case | Best for protecting devices on a controlled network | Ideal for remote workers and mobile users |
In factories, hardware firewalls give strong protection. They can filter traffic well and grow with your network. But they cost more and are harder to set up. If not managed well, they can be a single point of failure.
Advantages | Disadvantages |
|---|---|
Enhanced Security | Initial Cost and Investment |
Comprehensive Network Traffic Filtering | Configuration Complexity |
Scalability and Performance | Single Point of Failure |
Ease of Management | Limitations in Mobility and Remote Access |
Segmentation and Network Isolation | Potential Performance Impact |
Tip: Pick the firewall that fits your network’s size, needs, and budget.
Real-Time Threat Intelligence
Real-time threat intelligence keeps your firewall strong. Modern firewalls use automation to get updates about new threats. When a new bad website shows up, your firewall can update fast. This helps block attacks before they do harm.
You can use systems that collect logs and alerts from many tools. These systems check events as they happen. This helps your firewall find threats faster and more accurately.
Automation lets your firewall update itself when it finds new threats.
Centralized systems help your firewall see the big picture and react quickly.
Anomaly detection adds more safety. New systems use smart ways to find strange network behavior. These systems can find new attack types better than old ways. They use smart models to handle tricky network traffic and spot threats.
Note: Use real-time threat intelligence and anomaly detection to keep your firewall ready for new cyber threats.
Firewall Manufacturing Process

Material Selection
Building a firewall starts with picking good materials. The PCB is the base of every firewall. You need materials that let data move fast and keep signals strong. Good PCB materials help your firewall handle lots of traffic. They also help keep your network safe. You want materials that control heat well. This helps your firewall work smoothly, even when busy.
When you pick materials, you want them to last a long time. You want your firewall to protect your network for years. Strong materials stop signal loss. They help your firewall find threats fast. If you use weak materials, your firewall may slow down or stop working when you need it.
Tip: Choose PCB materials that are fast, cool, and last long. This makes your firewall more reliable.
PCB Manufacturing and Assembly
After picking materials, you start making the PCB. You design the PCB to connect all firewall parts. You put processors, memory, and network interfaces on the board. You make sure each part fits and works together.
During assembly, you solder each part onto the PCB. You check that every connection is strong. You test the board to see if it moves data fast. You want your firewall to handle traffic without delays. You also check for heat problems. If the board gets too hot, you add cooling.
You use network segmentation in your design. You split up different network areas on the PCB. This helps your firewall control traffic and block threats. You make sure each segment works with the others. This keeps your network safe and neat.
PCB Assembly Step | Purpose |
|---|---|
Component Placement | Connects firewall parts for smooth operation |
Soldering | Secures parts and ensures strong signals |
Testing | Checks speed, heat, and threat detection |
Segmentation Design | Supports network segmentation and safety |
Note: Careful PCB assembly helps your firewall stay fast and cool.
Quality Control and Compliance
You need strong quality checks to meet industry rules. You follow steps to check every firewall part. You start with a full audit plan. You gather and look at all firewall documents. You check firewall rules and settings. You see if your firewall matches standards like NIST Cybersecurity Framework, IEC 62443, and ISO 27001. These standards help keep data safe and your firewall strong.
You look at logs from your firewall. You run security tests to find weak spots. If you find problems, you fix them and test again. You use automated tools to help with checks. You keep records of every test and fix. You plan regular reviews to keep your firewall up to date.
Make a full audit plan for your firewall.
Gather and check all firewall documents.
Check firewall rules and settings.
Compare your firewall to industry standards.
Look at logs for signs of trouble.
Run security tests on your firewall.
Fix problems and test again.
Use automated tools for faster checks.
Keep records of all tests and fixes.
Review and update your firewall often.
You also follow rules from the NIS2 Directive. This means you manage risks and report any problems. You protect important systems and avoid penalties. You make sure your firewall stays strong and ready.
Alert: Regular checks and reviews keep your firewall safe from new threats.
Restrictive Traffic Rules
You set strict traffic rules to control data in your firewall. You use network segmentation to split up your network. You block traffic that should not be in some areas. You only allow safe and needed connections.
You write rules that limit who can reach sensitive zones. You stop outside traffic from getting to your main network. You use one-way rules to keep threats out. You update these rules often to match new threats.
Strict rules help your firewall block attacks.
Network segmentation helps you watch and control traffic.
Changing rules keeps your firewall strong as threats change.
Tip: Use strict traffic rules and network segmentation to keep your network safe and neat.
Next Generation Firewall Challenges
Common Pitfalls and Solutions
Setting up a next generation firewall can be hard. Misconfiguration is a big issue. If you use default passwords, attackers can get in easily. Sometimes, your firewall does not work well with your other hardware or software. This can slow things down and leave security holes. You should check for risks often and fix problems fast.
Picking the wrong size firewall makes it slow. Always look at your network traffic before choosing.
If you do not ask users what they need, you might miss something important.
Do not believe promises about future features. Pick what works now.
Make sure your firewall works with your current systems. This makes setup easier.
Choose a firewall that is simple to use and has good support.
Solution | Description |
|---|---|
Seamless configuration & policy management | Experts help set up your firewall and match rules to your needs. |
Advanced threat prevention | Use real-time updates and monitoring to stop new threats. |
Performance optimization | Deep packet checks and SSL decryption keep your firewall quick. |
False positive reduction | AI helps you get fewer alerts and focus on real dangers. |
Up-to-date security intelligence | Automatic updates and reviews keep your firewall ready. |
Enterprise-grade integration | Your firewall works with SIEMs, cloud, and identity systems. |
Innovations and Future Trends
New ideas are changing next generation firewalls. Firewall as a Service gives flexible protection for remote workers and offices. Cloud firewalls help protect cloud services. Hybrid mesh network firewalls mix different types for better security. Ken Wisniewski says, “Firewalls have become the ultimate positive security model tool in most enterprise networks, allowing only that which should be allowed.”
Artificial intelligence is making firewalls smarter. AI finds strange actions and new attacks right away. Your firewall can block bad traffic and keep risky devices away. AI also helps with deep packet checks and splitting up the network. This means better detection and faster response. AI firewalls can also quarantine devices and slow down odd data flows.
Feature | Description |
|---|---|
Threat Detection | AI quickly finds new threats and strange actions. |
Automated Responses | Your firewall can block and isolate risky devices by itself. |
Real-Time Traffic Analysis | AI helps check packets and understand apps in real time. |
Testing and Evaluation
You must test your next generation firewall before using it. Start by setting clear goals for your tests. Use both automatic scans and manual checks. Test your firewall from inside and outside your network. Update firewall rules often. Pretend real attacks to see how your firewall reacts.
Set clear goals for testing.
Use both automatic and manual checks.
Test from inside and outside your network.
Review and update firewall rules often.
Pretend real attacks to test your firewall.
You check your firewall with vendor tests, outside audits, and your own reviews. These ways help you see how your firewall works with network segmentation and other tools.
Metric/Method | Description |
|---|---|
Vendor Benchmarks | Show how your firewall works but may only test some attacks. |
Third-Party Technical Audits | Test security with many attack types and industry rules. |
Self-Assessments | Check how your firewall fits with your systems and real traffic. |
Tip: Careful testing helps you build a strong next generation firewall and a good security plan.
You help make strong cybersecurity firewalls. First, you plan and pick good materials. You test the firewall before using it. You set up logs and alerts to find problems fast. You use tough firewalls for hard places.
Advanced firewalls help stop data breaches.
Security tools work together to keep your network safe.
Cloud management and smart threat checks help you get ready for the future.
Be ready for new tech. Firewalls will get smarter to protect you from new cyber threats.
FAQ
What is a firewall in cybersecurity?
A firewall is a tool that stops bad network traffic. It can be a device or software. You use it to keep hackers and viruses away. Firewalls help keep your data and devices safe.
How do you choose the right firewall for your network?
First, look at how big your network is. Hardware firewalls are good for big networks. Software firewalls protect single devices. Pick a firewall that fits your security needs.
Why does PCB design matter for firewalls?
PCB design links all the firewall parts together. Good design makes your firewall fast and cool. Your firewall protects better when it works well and does not get too hot.
How often should you update firewall rules?
Check and update your firewall rules every month. New threats show up a lot. Updating often helps block new attacks and keeps your network safe.