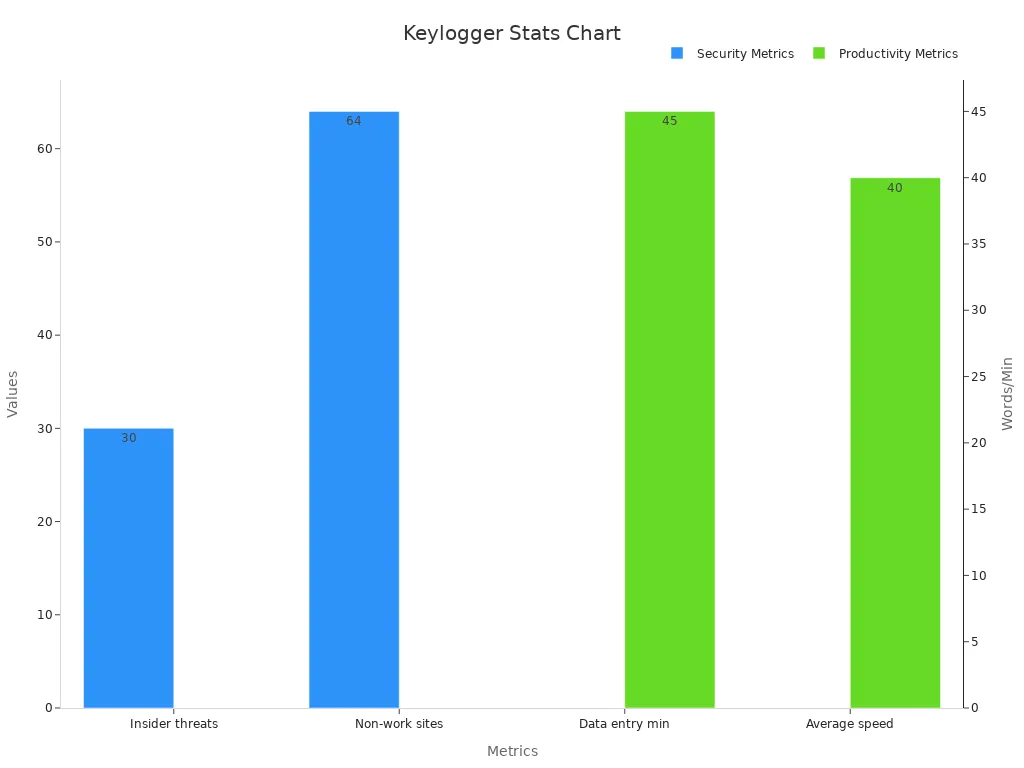
USB hardware keylogger development has many hard problems. These problems need careful work. Good keylogger devices help keep families and companies safe. Families use them for parental controls. Companies use them to find insider threats and check work. Keylogger technology can be used in two ways. This makes it important to design them ethically. They also need to work quietly. The chart below shows why monitoring is more important now. This is because insider threats and work problems are rising.
Engineers must keep working on usb hardware keylogger development. They need to make sure the devices stay small, safe, and work with new usb standards.
Key Takeaways
USB hardware keyloggers help keep families and companies safe. They record what people type on the keyboard quietly. They do not make the computer slow.
Making these devices is hard. They must be small and hard to see. They also need to work with many kinds of USB.
Keyloggers keep data safe by using encryption. They add a time to each keystroke. This helps give correct records for security checks.
Updates and smart design help keyloggers work well. They stay safe and can get new features later.
People must use keyloggers in the right way. It is important to follow laws and be fair. This helps keep trust and privacy at work and at home.
USB Hardware Keylogger Development
Purpose and Use Cases
USB hardware keylogger development helps people watch computer use at work and home. Companies use these devices to check what workers do. They want to keep important data safe and stop inside threats. Parents use keyloggers to keep their kids safe online. They also watch how their kids use the computer. A usb keylogger can record keystrokes before the computer starts. This makes it good for tracking all kinds of activity.
Keyloggers are important for safety and getting work done. They help companies make sure rules are followed. They also help parents teach kids to use computers the right way. But it is important to use them in a fair way. Bosses should tell workers about monitoring. Parents should keep a balance between safety and trust.
The table below shows the main ways usb hardware keyloggers are used:
Use Case Category | Corporate Data Protection | Parental Monitoring |
|---|---|---|
Purpose | Watch worker actions, find inside threats, protect company stuff | Watch kids’ computer use and online actions |
Legal/Ethical Framework | Must follow privacy laws and work rules | Needs to think about privacy and trust |
Monitoring Details | Record keyboard use, typing habits, and system use | Record what kids do, who they talk to, and online actions |
Deployment Notes | Needs to be put in place, should not be seen | Needs to be put in place, must be used fairly |
Security Needs
More people want usb hardware keyloggers because cyber threats are growing. Companies face more danger from inside threats and hardware attacks. In the last few years, usb device use went up by 30%. This gives hackers more chances to attack. Big data leaks, like at Equifax and Capital One, used keystroke loggers to steal private info.
Companies need usb keyloggers to see what users do on computers. These devices help track actions and support Zero Trust Hardware Access. Parents also use these tools to keep kids safe from online risks. Both groups need keyloggers that are quiet, work well, and follow the law.
Key Technical Challenges

Invisible Operation
A usb keylogger needs to stay hidden when it is used. It should not show up in system tools or warn users. Engineers make the keylogger so security software cannot find it. The device works without needing drivers or extra programs. This helps keep the keylogger secret and does not stop normal computer use. Being invisible is very important for safety and watching what happens. If people see the device, it cannot watch secretly anymore.
Note: When the keylogger is invisible, it does not slow down typing or the computer. People do not notice anything different.
Miniaturization
Making the usb keylogger small is a big challenge. The device has to fit inside a tiny usb plug. Engineers pick small parts and use special circuit designs. A small keylogger is easier to hide and put in place. Making it tiny also helps it look like other usb devices. The design must be small but still have enough memory and power. This lets the keylogger save lots of data without getting too big.
USB Compatibility
The usb keylogger must work with many usb types and devices. It needs to work with different keyboards and computers. It also has to work with usb hubs. Engineers test the device with many setups. They make sure the keylogger does not mess up the keyboard. Better compatibility lets the device work in more places. This makes it more helpful for companies and families.
Scalability
Scalability means the usb keylogger can get new features later. Engineers build the hardware and software so upgrades are easy. As technology gets better, the device can add more memory, encryption, and faster data moves. The table below shows how new features make the device better and more reliable:
Feature Added | Performance Improvement Description |
|---|---|
Increased Internal Memory (2MB to 16MB) | Stores more keystrokes, so it can save more data. |
SD Card Support | Gives more space for saving data for a long time. |
Real-Time Clock with Battery | Adds correct time stamps, even when the computer is off. |
Encryption | Keeps saved data safe from people who should not see it. |
Compatibility with USB Hubs | Works well with hubs, so the keyboard still works right. |
Flash Drive Mode (up to 125 kB/s) | Gets data quickly, so you do not wait long to see logs. |
Hardware/Firmware Optimization | Keeps the device hidden and stops typing delays. |
Scalability helps the keylogger stay useful as needs change. Companies and parents can use it for a long time. Upgrades help the usb keylogger stay good in a changing world.
Solutions in USB Keylogger Design

Hardware and Firmware
Engineers make each usb keylogger work on any computer. The device does not need extra software or drivers. It uses a small AVR microcontroller and a CPLD chip. These parts help the keylogger stay hidden and work fast. Developers use Atmel Studio and Quartus to write and test code. They update the hardware and firmware often. This helps them find and fix problems quickly. Studies show that automated testing and modular design make firmware safer. It also makes updates easier. Many companies now use over-the-air updates and secure boot features. These keep devices safe from attacks.
ProXray checks firmware for problems using symbolic execution.
Some systems use Mask Authentication Message and IPFS for safe updates.
Hardware security modules and trusted boot processes stop bad firmware.
Recording Keystrokes
The keylogger records every keystroke from the keyboard. It works before the operating system starts. This means it can record everything, even passwords before login. The device does not slow down typing or change how the keyboard works. Keylogger software often misses early keystrokes, but hardware keyloggers do not. The device uses special code to watch data and save each key press. This keeps the record complete and correct.
Note: Recording keystrokes at the hardware level gives a full picture of computer use.
Data Storage
The keylogger saves keystrokes in its NAND-flash memory. Some models let you use SD cards for more space. The device can save millions of keystrokes without running out of room. Users get the logs by typing a secret key combination. This keeps the data safe from people who should not see it. Engineers add encryption to protect the logs. They also use flash drive mode to let users download logs quickly. Keylogger software often uses the computer’s storage, but hardware keyloggers keep data safe even if the computer is wiped.
Storage Feature | Benefit |
|---|---|
NAND-flash memory | Saves millions of keystrokes |
SD card support | Adds more storage |
Encryption | Keeps logs private |
Flash drive mode | Fast log access |
Timestamping
A real-time clock with a battery gives each keystroke a time stamp. The clock works even when the computer is off. This helps users see when each event happened. Accurate time stamps make the logs more useful for security checks. Engineers use trusted hardware to keep the clock safe from tampering. Keylogger software sometimes guesses the time, but hardware keyloggers give exact records.
Tip: Timestamping helps track user actions and spot problems faster.
Engineers keep making hardware and firmware better. They use new tools and research to make keyloggers safer and more reliable. Companies like Tesla show that regular updates and smart design help devices stay ahead of threats.
Market Impact of Keylogger Innovation
Competitive Edge
Keylogger innovation changed how people watch computer use. Engineers fixed many hard problems. They made the device small, quick, and hard to find. These changes gave the product a big lead in the market. Many people want a tool that works on any computer. They also want it to work without extra software. The keylogger does both things. It works with many USB devices and keeps data safe.
A table below shows the top features that make this keylogger different from others:
Feature | Market Advantage |
|---|---|
Small size | Easy to hide and install |
OS-independent | Works on any system |
Fast data access | Quick log retrieval |
Secure storage | Keeps logs private |
Companies trust this device because it stays hidden and does not slow down computers. Parents like it because it helps keep children safe online.
Adoption and Use
Many groups now use this keylogger in real life. Sales numbers show that both businesses and families want it. Security teams use the device to watch for insider threats. Schools and parents use it to help kids use computers safely.
Engineers gave early versions to special partners. These partners tried the device at work and at home. Their feedback helped make the design better. After updates, the keylogger worked better and was easier to use. More people started using it as they saw its good points.
Businesses use the device to protect sensitive data.
Parents use it to monitor online activity.
IT teams value its easy setup and strong security.
The keylogger’s success comes from solving real problems and meeting user needs.
Solving tough problems in USB hardware keylogger development made the devices work better. They are now more reliable and safer. The table below shows these changes:
Aspect | Value | Explanation |
|---|---|---|
Reliability Index | 0.97 | Shows strong dependability |
Safety Index | 0.997 | Reflects high safety standards |
Technical Innovations | Modularization, AI, fault management | Boosts device performance and reliability |
Teams keep making the devices better by working on them often. Their skills help them handle new dangers. This way, the products stay useful and safe as things change.
FAQ
What is a USB hardware keylogger?
A USB hardware keylogger is a tiny device. It records every key you press on a keyboard. You plug it between the keyboard and the computer. Many groups use it to watch what people type. They use it to help keep things safe.
Can antivirus software detect a USB hardware keylogger?
Most antivirus programs cannot find a USB hardware keylogger. This device works outside the computer’s main system. To find it, people must look at the USB ports. They need to check for anything that does not belong.
How can someone detect and remove a keylogger from their computer?
People should look at all USB connections for strange devices. They can unplug anything that looks odd or extra. Security teams teach workers how to spot and remove keyloggers. They do this during regular checks at work.
Is using a USB keylogger legal?
The law changes based on where you live and why you use it. Companies must follow privacy rules and tell workers about monitoring. Parents should think about their kids’ privacy too. Always check the law before using these devices.
What makes USB hardware keyloggers different from software keyloggers?
USB hardware keyloggers work by watching the keyboard itself. They do not need any software or drivers to work. Software keyloggers run on the computer and can be stopped by security tools.